Average Data Breach Costs $3.8 Million, Ponemon Finds

When an organization's records are breached, it costs an average of $3.8 million to overcome the attack, according to the newly released Ponemon Institute's "Cost of Data Breach Study: Global Analysis."
Ironically, the annual report came out the day after the Internal Revenue Service disclosed hackers used stolen data to access the records of more than 100,000 taxpayers. The IRS paid out more than $50 million in fraudulent tax returns before discovering the crime, the IRS reported.
The average cost an organization incurs for each lost or stolen record grew 6 percent between 2013 and 2014, to $154 from $145, Ponemon said. But healthcare organizations could pay more than double: the average cost for data-loss within healthcare firms reached up to $363 on average, the IBM-sponsored study determined. Retailers, too, saw a large increase, with the average cost of stolen records surging to $165 from $105 in last year's study. Within education, the cost can reach $300 per record, but the lowest cost per record is in transportation (at $121) and public sector (at $68), Ponemon said.
"Based on our field research, we identified three major reasons why the cost keeps climbing," said Larry Ponemon, chairman and founder, Ponemon Institute, in a statement. "First, cyber attacks are increasing both in frequency and the cost it requires to resolve these security incidents. Second, the financial consequences of losing customers in the aftermath of a breach are having a greater impact on the cost. Third, more companies are incurring higher costs in their forensic and investigative activities, assessments and crisis team management."
Hackers and criminal insiders cause the most costly damage; the average cost per record to resolve those attacks is $170, the study found. And these bad actors caused 47 percent of all breaches in this year's report, Ponemon said. But other causes are not inexpensive: System glitches cost $142 per record, while human error or negligence cost $137 per record, the study showed.
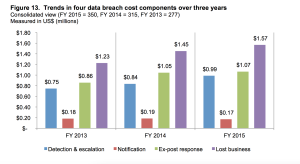
The cost of recovery is increasing, even as notification costs drop to $170,000 this year from $190,000 in 2013. Lost business costs – which include increased customer turnover, higher customer acquisition costs, reputation damage, and diminished goodwill – grew to $1.57 million in 2015 versus $1.23 million in 2013, the report said.
The faster an organization discovers and mitigates damage, the better it is – for the company, its customers, and partners, Ponemon found. However, malicious attacks take an average of 256 days to discover and those caused by human error take an average of 158 days to identify, the study said.
One reason it can take so long?
"Many clients still do not have the tools, automated processes, and expertise in place to identify breaches; or they have some in place but they can become obsolete fast in a world where the technology is transforming (cloud, mobility) and where also 'bad guys' are highly organized crime rings, very innovative and very sophisticated," said Laurence Guihard-Joly, general manager of Resiliency Services at IBM Global Technology Services. "Sometimes enterprises and organizations are working too much in a silo mode, and there is not enough unity in the security teams across their units. Having an effective business continuity plan in place reduced the mean time to identify a data breach by 27 percent and the mean time to control a data breach by 41 percent."
An Ounce of Prevention
A well-educated and aware leadership team is an invaluable asset in an organization's cybersecurity initiatives, according to the report. If the board takes an active role when an organization has a breach, the cost is reduced by $5.50 per record; when organizations purchase insurance protection, the costs drop by $4.40 per record, Ponemon found.
"There is a growing awareness and involvement at the c-Level and the board of directors, driven by the risks on reputation – today when something wrong happens, it becomes public extremely fast through social networks etc. – and loss of revenue," said Guihard-Joly. "And this is true for all sizes of business. But there are still a lot of c-level business leaders who still consider that it can happen to others, but won't happen to me. It is clear that we still need to accelerate our collaboration and knowledge within the industry."
It's also vital for internal IT departments to extend collaboration beyond their walls and throughout business divisions, into the upper echelons of the boardroom, labs, and engineering departments that may operate outside IT. Ongoing tests to ensure emergency plans work are critical. After all, security cannot go rogue, experts agreed.
"This is primarily a 'business' discussion that must be connected to the enterprise risk management program. Conduct a comprehensive assessment of their current security and business resilience posture, focused on impact-based analysis of threats, connect with business strategy, engage the c-suite, prioritize, and make it also a company program where each employee feels in charge of the security and resiliency," said Guihard-Joly. "Cybercrime will not go away soon. But there are ways to protect yourself."