3 Steps to Boost Healthcare Data Security

Security breaches are on the rise, and it’s become not a question of if, but when, an organization will be hacked.
According to the U.S. Department of Health and Human Services, citing a study by Kaiser Permanente in California and Stanford University, breaches in data security exposed more than 29 million health records to potential criminal misuse between 2010 and 2013. While researchers found that the majority of breaches involved simple theft of a computer with sensitive information, they found that electronic health records also are increasingly vulnerable to exposure through hacking activity.
A 2015 Ponemon Institute study revealed that criminal attacks -- the deliberate attempt to gain unauthorized access to sensitive information resulting in compromised data – in the healthcare sector have risen 125 percent since 2010 and are now the leading cause of a data breach. What’s especially alarming is that a full 65 percent of all healthcare organizations have experienced an electronic information-based security incident during the past two years alone, says the Ponemon study.
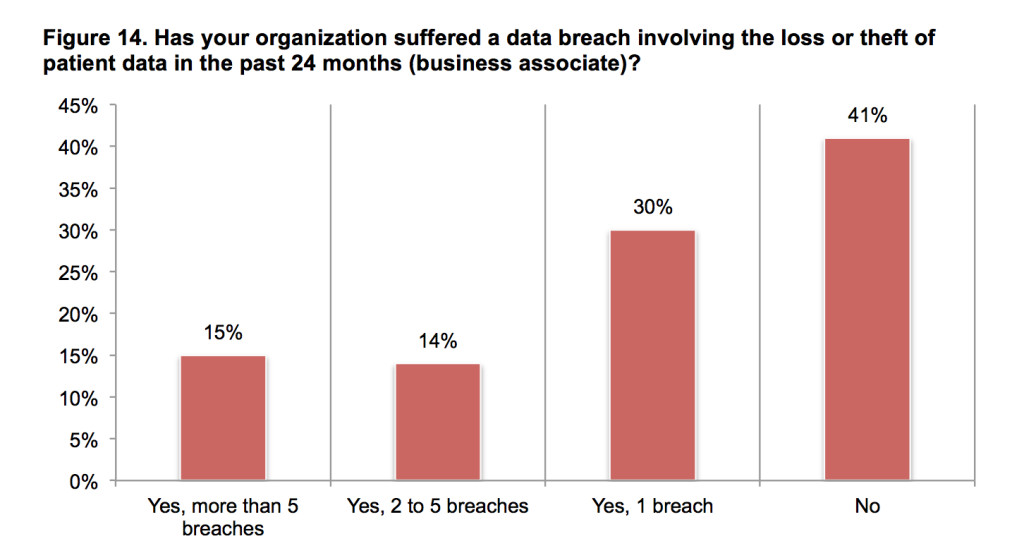
(Source: Ponemon Institute's Fifth Annual Benchmark Study on Privacy & Security of Healthcare Data)
While the number and severity of criminal attacks are on the rise, most healthcare organizations still remain underprepared to address the rapidly-changing cyber threat environment. Healthcare’s security levels have fallen behind other verticals.
No organization wants to be the focus of security investigations and negative publicity, much less costly litigation. Investment in security measures is seen as insurance against these risks, but providers are also concerned with security investments draining an already-slim profit margin. Current challenges -- working with big data, proliferating medical devices, the need to provide real-time access to patient information, regulatory compliance, securing protected health information (PHI) and the expanding scope of mobile devices and applications, as well as intense pressure to cut costs while boosting efficiencies wherever possible – all combine to make IT security especially challenging for healthcare organizations. However, focusing on data security has become absolutely imperative.
TCS recently commissioned a survey across a broad segment of roles within healthcare payers and provider organizations to gain a deeper understanding of healthcare provider challenges and priorities. According to survey findings, data security is now the number one technology imperative for healthcare organizations, and the highest provider CIO mandate.
Understanding the organization must take action and knowing exactly where to focus its IT efforts to ensure optimal data security are two different things. With so many forces complicating the healthcare security picture, it’s not easy to decide what security measures to take and where to begin.
A good starting point is to laser focus on the data elements instead of attempting to secure their whole operating environment. Superior data security requires provider organizations to understand the data and get a handle on who has permission to view each data element, and then put a plan in place to prevent intruders from using it. Healthcare organizations can more effectively deal with data security by following a three-step process:
Step one: Assess infrastructure down to the data level and identify areas of exposure. Providers need to fully understand their data and where it resides – and identify what would be at risk if that data gets into the hands of fraudsters. Unfortunately, most providers currently don’t have a good handle on this and haven’t yet done an in-depth analysis of their system and their vulnerabilities. It’s quite possible that they’re focusing their efforts on the wrong things.
All providers have at least overall minimum security standards in place that include things like password protection and identity authentication. What they may not have examined is the data itself and the ramifications to the organization if the certain data elements get out.
Step two: Prioritize who has access to the data. Once an organization has done an infrastructure assessment, it must determine the frequency at which the data is being released within the company, who has the right to see it, and why these individuals need to have access to it. It’s critical to identify employees who have permission to different pieces and combinations of data, and look at the purpose that data exposure serves. Determine if different mixtures of individual data elements need to be protected from getting into the wrong hands.
Step three: Mask individual data elements so they can only be identified by proper, authorized users. Data masking gives hackers a package of valueless data so if information gets into the hands of a person or entity trying to hack the system. Give out data in such a way that even if the data is breached, it’s not going to be usable. For instance, if a fraudster needs to collect three pieces of data to put together a person’s identity, protect individual elements from being accessed in a toxic combination.
It’s no longer realistic for an organization to believe it has superior data security and can never be hacked. These days, it’s become a given that you’re going to be breached. The idea is to understand what would happen if each specific data element gets out alone or in combination with other pieces, how fast you can react, and change, tag or alter one or more of those data elements to prevent intruders from getting at it and using it for nefarious purposes.
About the Author:
 Magna Hadley is Global Head, Healthcare Domain Practice at Tata Consultancy Services (TCS). Magna has over 25 years’ experience in defining and leading the delivery of strategic business solutions and technology-enabled transformations. She is internationally-recognized as a dynamic strategist of business growth and profitability and has extensive experience in leading large-scale systems implementations, driving initiatives to optimize efficiencies and maintaining performance quality. Follow Tata on Twitter @TCS_NA.
Magna Hadley is Global Head, Healthcare Domain Practice at Tata Consultancy Services (TCS). Magna has over 25 years’ experience in defining and leading the delivery of strategic business solutions and technology-enabled transformations. She is internationally-recognized as a dynamic strategist of business growth and profitability and has extensive experience in leading large-scale systems implementations, driving initiatives to optimize efficiencies and maintaining performance quality. Follow Tata on Twitter @TCS_NA.
Related
Managing editor of Enterprise Technology. I've been covering tech and business for many years, for publications such as InformationWeek, Baseline Magazine, and Florida Today. A native Brit and longtime Yankees fan, I live with my husband, daughter, and two cats on the Space Coast in Florida.










