Overcoming the 3 Key Barriers to Industrial IoT
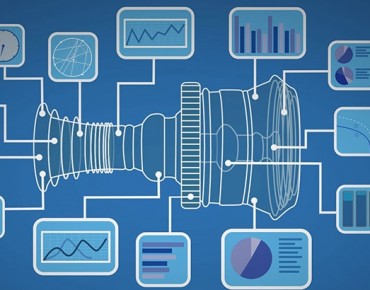
The Industrial Internet of Things (IIoT) offers exciting possibilities for transforming industrial automation. Having the ability to capture data at the industrial edge—from the manufacturing shop floor to natural gas compression stations in the field—offers the ability to leverage Big Data analytics to optimize operations, streamline efficiency and generate insights that increase profitability and competitive advantage.
So why aren’t we seeing more IIoT implementations?
Here are three of the major barriers slowing adoption of IIoT in industrial automation, along with strategies for overcoming them:
- Conservative Technology Culture
A major barrier has to do with the mindset and culture of Operational Technology (OT) organizations, which is quite different from those of IT organizations. Whereas IT is defined by constant change and innovation, OT is change- and risk-averse. That’s why it’s not unusual to see industrial automation systems in service for decades at a time with little or no change. In a world where any downtime of production systems can have a devastating impact on revenue — not to mention one’s career — stability is the top priority.
Achieving the full potential of IIoT means bridging the gap between these two cultures, so that competing IT and OT priorities are met. Indeed, we’re beginning to see the emergence of a new breed of “industrial technologists,” who bring a combined IT/OT perspective to the enterprise. They understand that for IIoT to be a viable reality, the need for “always on” availability must be met. Moreover, this must be achieved without dramatically increasing operational complexity and increasing the burden on lean OT staffs.
- Monetization Questions
Industrial technology investments are highly ROI-driven. This is especially true in industries where margins are thin and in smaller organizations, where cash may be in short supply. Unless decision-makers can see a clear path to monetizing new technologies in 12 months or less, these investments are generally non-starters.
OT organizations are familiar with SCADA (Supervisory Control And Data Acquisition) systems that provide remote monitoring and control of equipment. For example, a SCADA system in a chemical plant might monitor a process to ensure the correct mixture of raw materials and/or proper temperature is maintained. The idea of using data for anything other than running or monitoring production systems is a foreign concept.
The IIoT changes this paradigm. Now, data gathered via sensors throughout the plant can be captured and analyzed to provide a wealth of new insights. Example: predictive maintenance. Analyzing a wide range of operational parameters from individual equipment components can help predict failures before they occur, minimizing unplanned downtime. This also reduces planned downtime, helping identify the optimum maintenance or replacement intervals based on actual operational conditions, rather than a vague mean-time-before-failure (MTBF) specification in a manual. Over time, the value of predictive maintenance alone could be significant. And that’s just one obvious example of the IIoT at work.
Of course, achieving these benefits requires continuous, uninterrupted data to fuel the analytics. Ensuring data integrity and completeness is essential. That means these IIoT systems and data stores must deliver a high degree of fault tolerance.
- Cybersecurity Concerns
As noted, stability is the first priority for OT personnel. To minimize the risk of security intrusions or interactions that could cause downtime, industrial automation systems are often “walled off” from the rest of the enterprise IT infrastructure. But connectivity and interoperability are the keys to the IIoT, which often involves cloud technologies. How can industrial enterprises tap the benefits of the IIoT while addressing their operational security concerns?
First, it’s important to recognize that IIoT implementations are not, by definition, cloud-based — at least, not public cloud-based. Large enterprises in many industries have established private cloud infrastructures that provide the security required for mission-critical applications. Another secure approach: an IIoT implementation could leverage a secure corporate network with no “doors” to the outside world; effectively, a data-center-based approach. These approaches can ensure SCADA data has the level of protection it requires.
It’s also important to recognize that the sensors deployed to collect data need not interact with SCADA data. IIoT sensors effectively serve as “one-way” communication nodes that do not directly impact processes, minimizing security risks.
Despite these realities, it would be naive to say that the IIoT does not introduce potential vulnerabilities compared to a “walled off” infrastructure. The important point is that security challenges can be overcome, enabling the benefits of an IIoT implementation outweigh the risks. The key is in deploying any new IIoT elements with a keen eye on minimizing potential vulnerabilities affecting security and availability.
John Fryer is senior director of product marketing at Stratus Technologies.










