The Week in Cybersecurity: Kaspersky Out in the Cold; Azure Releases ‘Confidential Computing’

(deepadesigns/Shutterstock)
Cybersecurity – along with national security and Russian espionage – are very much in the news, and the two concerns came together this week with the announcement by the U.S. Department of Homeland Security that federal agencies stop using security products made by Russian software company Kaspersky Lab. The concern: using Kaspersky anti-virus software, under influence from the government of Russian president Vladimir Putin, could be a national security threat.
Put another way, Kaspersky cybersecurity applications might be “turned” and made to work, in effect, as double agents within our national government agencies and corporations. It feels like 1962 all over again. Adding to the retro Cold War feel: the great John le Carré has produced a new book (a very good one – ed.) concerned, as always, with “moles” conducting surveillance from the inside of our intelligence apparatus – precisely the potential problem with Kaspersky.
 However, at least one industry analyst, Bob Sorensen of Hyperion Research (formerly with IDC), said the Kaspersky problem is not uncommon – and that banning Kaspersky is part of a widespread and misplaced confidence in “safe” supply chains.
However, at least one industry analyst, Bob Sorensen of Hyperion Research (formerly with IDC), said the Kaspersky problem is not uncommon – and that banning Kaspersky is part of a widespread and misplaced confidence in “safe” supply chains.
“The IT sector has become globalized to the point where I suspect that there is not any significant hardware or software product on the market today that at some point in its design or manufacture did not pass through a number of nations, some that would raise issues of US national security concern,” he told EnterpriseTech In an email. “As a result, the desire of having a US-only assured supply chain for US government (USG) consumption, or one that consists of only trusted allies, is long obsolete.”
He also noted that US-based technology is no guarantee of 100 percent security, and said the Kaspersky ban “is, in reality, ultimately dangerous as it gives a false sense of confidence that U.S. national security interests are being protected from foreign threats, when in fact such bans do not really address the realities of US dependencies on foreign supply chains.”
The real need, he said, is to concentrate efforts on hardware and software technology that is designed from the outset to deal with untrusted components and uncertain vendors. “Rather than barring suspected outsiders at the gate, cyber security policy needs to drive development of a new cyber security paradigm that instead seeks to build tightly bound, system-wide cyber security infrastructures that are baked into an entire IT system.”
Infrastructures should be built with “no single point of failure – either intentional or unintentional – and internal security controls would be specifically designed to accept and handle rogue software or hardware elements in an efficient and secure manner,” Sorensen said.
 Another significant cybersecurity development this week: Microsoft announced yesterday the availability on its Azure cloud platform of “confidential computing,” the encryption of data while in use, “a protection that to date has been missing from public clouds,” according to Microsoft CTO Mark Russinovich.
Another significant cybersecurity development this week: Microsoft announced yesterday the availability on its Azure cloud platform of “confidential computing,” the encryption of data while in use, “a protection that to date has been missing from public clouds,” according to Microsoft CTO Mark Russinovich.
Microsoft said the capability, available via an Early Access program for Azure SQL Database and SQL Server, was developed by a team at Azure along with several groups within Microsoft and Intel for the past four years.
“While many breaches are the result of poorly configured access control, most can be traced to data that is accessed while in use, either through administrative accounts, or by leveraging compromised keys to access encrypted data,” Russinovich said.
He said confidential computing protects against a variety of threats, including: malicious insiders with administrative privilege or direct access to hardware on which it is being processed, hackers and malware that exploit bugs in the operating system, application, or hypervisor, and third parties accessing it without consent.
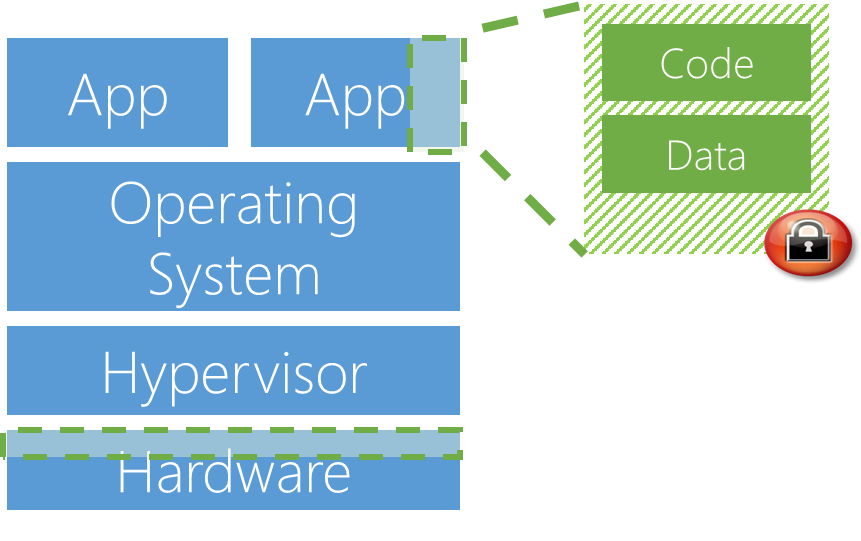
The key to confidential computing is ensuring that when data is “in the clear,” required for efficient processing, it is protected within a Trusted Execution Environment (TEE - also called an enclave), which makes it impossible to view data or inside operations from the outside, even with a debugger.
“They (TEEs) even ensure that only authorized code is permitted to access data,” Russinovich said. “If the code is altered or tampered, the operations are denied and the environment disabled. The TEE enforces these protections throughout the execution of code within it.”
The significance of Azure confidential computing is that it can be used with a variety of TEEs without having to change their code. Russinovich said that, initially, Azure will support two TEEs, Virtual Secure Mode and Intel SGX, and will work with Intel and other hardware and software partners to develop additional TEEs and will support them as they become available.
Russinovich said confidential computing has applicability in, for example, finance, where personal portfolio data and wealth management strategies would no longer be visible outside of a TEE. Healthcare organizations can share private patient data, like genomic sequences, to gain insights from machine learning across multiple data sets, without risk of data being leaked to other organizations. In oil and gas, and IoT scenarios, sensitive seismic data that represents the core intellectual property of a corporation can be moved to the cloud for processing, but with the protections of encrypted-in-use technology.
TEEs and enclaves are not new to Microsoft. The company already uses them to protect blockchain financial operations (Coco Framework), data stored in SQL Server and its own infrastructure within Azure, Russinovich said.