Spectre, Meltdown Redux: Intel Chips Found Vulnerable to More Malware

via Shutterstock
A published report states that Intel chips are vulnerable to three new malware attacks with the ability to steal passwords, personal information, financial data and encryption keys. Intel has confirmed the report on its Software Developer Zone site, giving the malware a “high severity” rating.
According to Intel, the malware can mount “side channel” attacks of cached data triggered by “terminal faults” and affects microprocessor products supporting Intel Software Guard Extensions.
“Accessing a logical or linear address that is not mapped to a physical location on the hardware will result in a terminal fault,” Intel stated on it Developer Zone page. “Once the fault is triggered, there is a gap before resolution where the processor will use speculative execution to try to load data. During this time, the processor could speculatively access the level 1 data cache (‘a small pool of memory within each processor core designed to store information about what the processor core is most likely to do next’), potentially allowing side-channel methods to infer information that would otherwise be protected.”
According to a story in the U.K.-based technology trade publication The Register, Intel desktop, workstation, and server CPUs are all vulnerable to what Intel calls the L1 Terminal Fault. The news comes after disclosures late last year of two other similar side channel malwares, Spectre and Meltdown. Intel released patches early this year to combat the vulnerabilities, and protection against Spectre and Meltdown are built into next-generation Xeon chips Intel will release later this year.
To protect against L1 Terminal Fault now, Intel said it has released new microcode for many processors affected by L1TF. “This modifies some operations to implicitly remove data from the L1D during certain privilege transitions.” But this and other microcode updates, Intel warned, “is not sufficient to protect against L1TF. Deploying OS and VMM updates is also required…”
“The microcode updates released earlier this year when coupled with operating system and hypervisor software available from our industry partners, ensure consumers, IT professionals and cloud service providers have access to the protections they need,” the company said. “Intel recommends people keep their systems up to date to protect against the evolving threat landscape.”
Intel said that the L1TF threat was first reported to the company by researchers at KU Leuven University, Technion – Israel Institute of Technology, University of Michigan, University of Adelaide and Data61, adding that “We are not aware of reports that any of these methods have been used in real-world exploits, but this further underscores the need for everyone to adhere to security best practices. This includes keeping systems up-to-date and taking steps to prevent malware.”
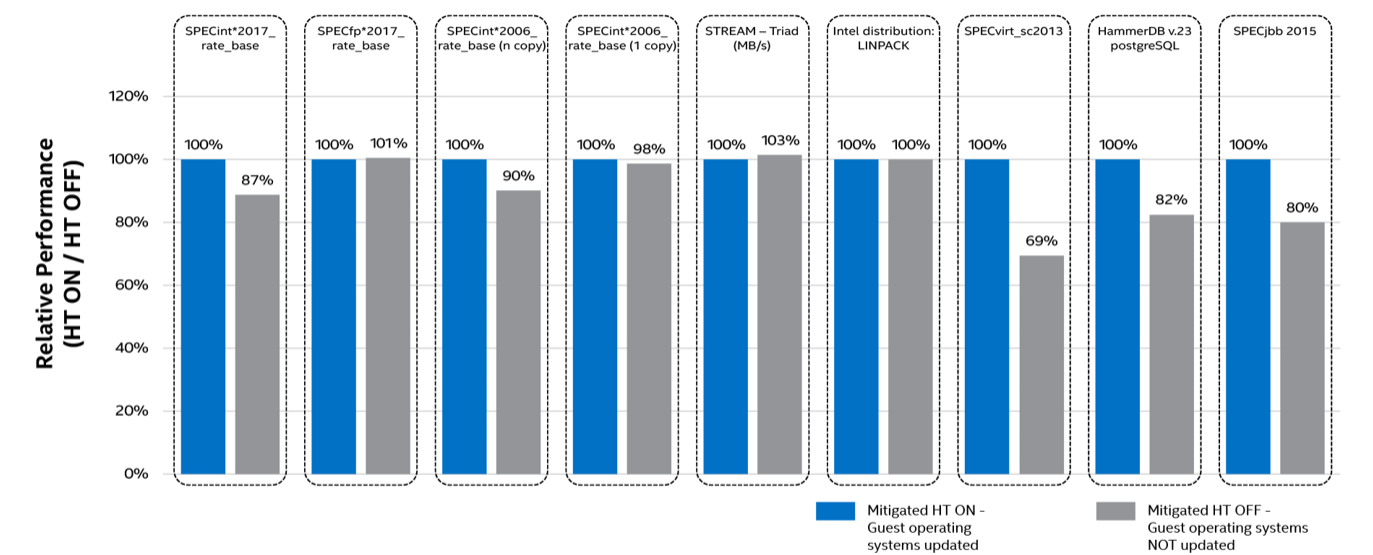
As for impact on performance, Intel said “there has been no meaningful performance impact observed as a result of mitigations applied.” However, for “a subset of those running traditional virtualization technology, and primarily in the data center – it may be advisable that customers or partners take additional steps to protect their systems... to safeguard against situations where the IT admin or cloud provider cannot guarantee that all virtualized operating systems are protected. Deciding to take additional steps depends on the system software in use, the workload, and the customer’s assessment of the security threat model for their environment.”
Below is an Intel chart showing performance impact on data center workloads “where it cannot be guaranteed that all virtualized guest operating systems have been updated”: